Discover the implementation details of MASC, focusing on modularity, automation, and flexibility to effectively detect and analyze crypto-API misuses.
Authors: Amit Seal Ami, Computer Science Department, William & Mary Williamsburg, Virginia, USA, and this author contributed equally to this paper ; Syed Yusuf Ahmed, Institute for Information Technology, University of Dhaka Dhaka, Bangladesh, and this author contributed equally to this paper ; Radowan Mahmud Redoy, Institute for Information Technology, University of Dhaka Dhaka, Bangladesh, and this author contributed equally to this paper ; Nathan Cooper, Computer Science Department,...
Authors: Amit Seal Ami, Computer Science Department, William & Mary Williamsburg, Virginia, USA, and this author contributed equally to this paper ; Syed Yusuf Ahmed, Institute for Information Technology, University of Dhaka Dhaka, Bangladesh, and this author contributed equally to this paper ; Radowan Mahmud Redoy, Institute for Information Technology, University of Dhaka Dhaka, Bangladesh, and this author contributed equally to this paper ; Nathan Cooper, Computer Science Department,...
South Africa Latest News, South Africa Headlines
Similar News:You can also read news stories similar to this one that we have collected from other news sources.
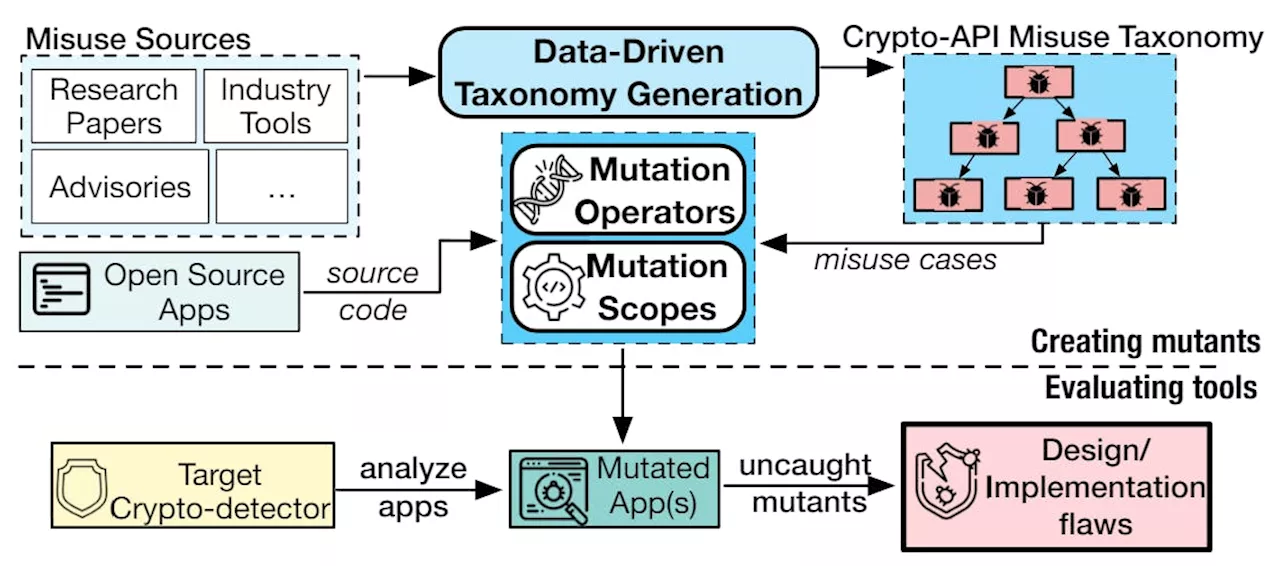 MASC: A Tool for Mutation-Based Evaluation of Static Crypto-API Misuse DetectorsLearn about MASC, an advanced tool designed for evaluating crypto-detectors, identifying crypto-API misuse, and enhancing software security.
MASC: A Tool for Mutation-Based Evaluation of Static Crypto-API Misuse DetectorsLearn about MASC, an advanced tool designed for evaluating crypto-detectors, identifying crypto-API misuse, and enhancing software security.
Read more »
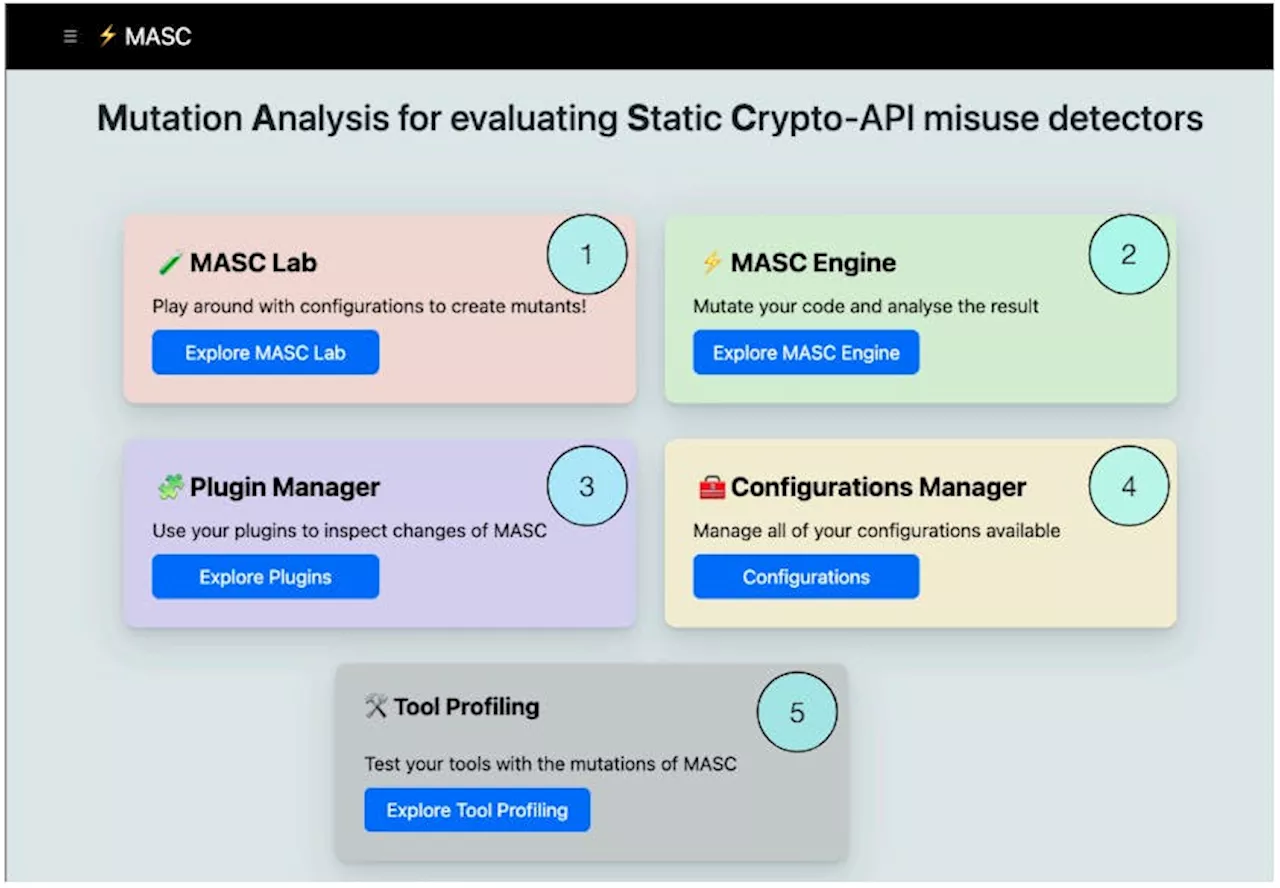 MASC User Guide: Experiment, Mutate, and Analyze Crypto-API MisusesLearn how to use MASC via command line and web interfaces for testing and analyzing crypto-API misuses in software development.
MASC User Guide: Experiment, Mutate, and Analyze Crypto-API MisusesLearn how to use MASC via command line and web interfaces for testing and analyzing crypto-API misuses in software development.
Read more »
 The Road Ahead for MASC: Expanding Crypto-API Misuse DetectionExplore the future enhancements and concluding insights of MASC, focusing on extending customization and evaluating additional crypto-detectors.
The Road Ahead for MASC: Expanding Crypto-API Misuse DetectionExplore the future enhancements and concluding insights of MASC, focusing on extending customization and evaluating additional crypto-detectors.
Read more »
 MASC's Three Mutation Scopes for Comprehensive Crypto-API Misuse AnalysisDiscover how MASC's Main, Similarity, and Exhaustive Scopes enhance the detection of crypto-API misuses in software development.
MASC's Three Mutation Scopes for Comprehensive Crypto-API Misuse AnalysisDiscover how MASC's Main, Similarity, and Exhaustive Scopes enhance the detection of crypto-API misuses in software development.
Read more »
 How MASC Mutation Operators Bridge Security Gaps in Crypto-API UsageLearn how MASC uses generalizable mutation operators to detect crypto-API misuse, improving the robustness of crypto-detectors.
How MASC Mutation Operators Bridge Security Gaps in Crypto-API UsageLearn how MASC uses generalizable mutation operators to detect crypto-API misuse, improving the robustness of crypto-detectors.
Read more »
 Smart Supply Chain Management: Implementing IoT Technologies To Optimize Supply Chain VisibilityPrzemek Szleter is the founder and CEO of DAC.digital, with over 16 years of professional experience as a business & IT executive. Read Przemek Szleter's full executive profile here.
Smart Supply Chain Management: Implementing IoT Technologies To Optimize Supply Chain VisibilityPrzemek Szleter is the founder and CEO of DAC.digital, with over 16 years of professional experience as a business & IT executive. Read Przemek Szleter's full executive profile here.
Read more »